Tech
What Is A Trojan Horse And How To Protect Your Computer From Trojan Horses?

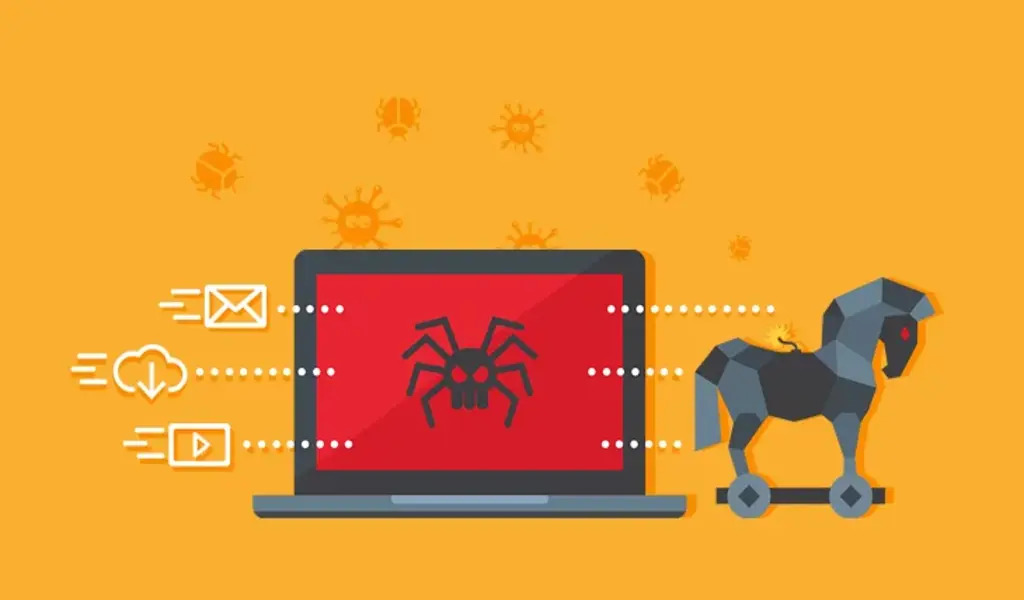
What is a Trojan Horse? – With the rise of technology, the risk of cyber threats has also increased. The Trojan horse is among the most harmful forms of malware that threatens computer security.
It presents itself as genuine software but once installed, it can cause severe damage to your system.
This article aims to educate you about the nature of a Trojan horse, its mode of operation, and essential tips to safeguard against this malicious program
What is a Trojan Horse?
Malware known as a Trojan horse appears to be a genuine program or file, like a game or software update.
Once a user installs the Trojan horse, it can execute several harmful actions, such as stealing confidential information, erasing files, or commanding the computer system.
In contrast to viruses, Trojan horses do not self-replicate and depend on users for installation.
Types of Trojan Horses
To reach particular objectives, there are several types of Trojan horses created. Here are some of the commonly used ones:
Remote Access Trojans (RATs)
Hackers aim to gain entry to the infected computer using Remote Access Trojans. The hacker can exercise full control over the device once installed and can engage in a range of nefarious activities.
Banking Trojans
Sensitive data such as banking login credentials, credit card data, and additional financial information are acquired by Banking Trojans.
Backdoor Trojans
Backdoor Trojans establish an entrance into the infected computer system, enabling hackers to remotely access and manage it.
How to Protect Your Computer from Trojan Horses
Consider following these guidelines to safeguard your computer from Trojan horses:
Use Antivirus Software
To shield your computer from harmful software such as Trojan horses, use antivirus programs.
Always keep your antivirus software up-to-date and perform frequent scans on your computer for viruses and other malevolent programs.
Be Cautious When Downloading Software
It is crucial to download software only from reliable sources. Stay away from obscure or questionable sites. Before installing any software, carefully go through reviews and rating to assure its credibility.
Keep Your Operating System and Software Updated
To safeguard your computer against potential hacks, it is crucial to ensure that both your software and operating system are kept up to date with the latest security patches.
These updates can effectively shield your system from known vulnerabilities that may be exploited by hackers.
Use a Firewall
To prevent unauthorized access to your computer system, ensure your firewall is correctly configured and switched on.
Use Strong Passwords
It is recommended to utilize robust and intricate passwords that are not easy to deduce. Refrain from utilizing the identical password for various accounts and make it a habit to frequently modify your passwords.
Be Cautious of Email Attachments and Links
It is advisable to exercise caution while opening email attachments or clicking on links in emails, particularly if they originate from doubtful or unfamiliar senders.
Trojan horses have the potential to proliferate via email attachments or links.
Conclusion
To safeguard your computer system against malware, particularly the perilous Trojan horse, it’s essential to adhere to the suggestions mentioned in this write-up.
Utilize antivirus tools, exercise caution while downloading software, ensure routine updates of the operating system and software, integrate a firewall, implement secure passwords, and handle email attachments and links with discretion.
These measures will aid in averting any significant harm to your computer.
FAQs
- What distinguishes a virus from a Trojan horse? While a virus is a kind of malicious software that infects additional files by replicating itself, a Trojan horse disguises itself as genuine software.
- Can a Trojan horse pilfer sensitive information? Yes, Trojan horses are capable of stealing sensitive information including credit card data, banking login credentials, and other confidential data.
- Will antivirus software detect every kind of Trojan horse? Not all antivirus software programs will be able to identify every type of Trojan horse. So, it’s crucial to use reliable antivirus software and regularly update it to shield against emerging threats.
- How do Trojan horses spread throughout systems? Trojan horses can spread through phony emails, application downloads, and infected websites.
- What should I do if I think my system has been seized by a Trojan horse? If you suspect that your system has been infiltrated by a Trojan horse, immediately disconnect it from the internet and run a virus scan with antivirus software. You may need to engage professional help to eradicate the Trojan and rectify any damage it has caused.
RELATED CTN NEWS: